SHA-1 Generator – Efficient 160-Bit Hashing for Data Integrity
Created on 27 October, 2025 • Generator Tool • 4 views • 2 minutes read
SHA-1 generator is a tool or software component that computes the SHA-1 (Secure Hash Algorithm 1) cryptographic hash function, producing a fixed 160-bit (20-byte) hash value from any input data.
A SHA-1 generator is a tool or software component that computes the SHA-1 (Secure Hash Algorithm 1) cryptographic hash function, producing a fixed 160-bit (20-byte) hash value from any input data. This hash, often displayed as a 40-character hexadecimal string, serves as a unique digital fingerprint of the input, enabling data integrity verification, digital signatures, and other security-related applications.
Understanding SHA-1
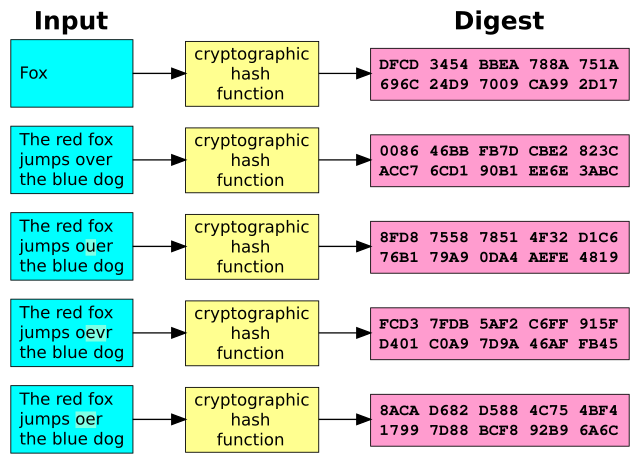
SHA-1 was designed by the United States National Security Agency (NSA) and published in 1995 as part of the Secure Hash Standard. It processes input data in 512-bit blocks through 80 rounds of complex bitwise operations, including logical functions, modular additions, and bit rotations, following the Merkle–Damgård construction. The output is a 160-bit digest that changes drastically even if a single bit of the input is altered, demonstrating the avalanche effect.
Why Use a SHA-1 Generator?
Despite being cryptographically broken and vulnerable to collision and length extension attacks, SHA-1 remains in use for legacy systems and non-critical applications due to its speed and widespread support. A SHA-1 generator is useful for:
* Verifying file integrity where legacy checksums are required.
* Generating unique identifiers or fingerprints for data.
* Supporting older digital signature schemes still in operation.
* Educational and testing purposes in cryptography.
Features of a Reliable SHA-1 Generator
* Fast and Efficient: Processes large files and data streams quickly with minimal memory usage.
* Cross-Platform Support: Available in most programming languages and operating systems.
* Multiple Input Types: Accepts text, files, or streamed data.
* Output Formats: Provides hash output in hexadecimal, base64, or binary formats.
* Batch Processing: Supports hashing multiple files or inputs in one operation.
How to Use a SHA-1 Generator
Generating a SHA-1 hash from text:
bashDownloadCopy codesha1-gen --text "Hello, World!"
# Output: 2ef7bde608ce5404e97d5f042f95f89f1c232871
Hashing a file:
bashDownloadCopy codesha1-gen --file /path/to/file.txt
Using SHA-1 in code (Python example):
pythonDownloadCopy codeimport hashlib
def sha1_hash(data: bytes) -> str:
return hashlib.sha1(data).hexdigest()
print(sha1_hash(b"example"))
Security Considerations
SHA-1 is no longer recommended for security-sensitive applications due to demonstrated vulnerabilities, including practical collision attacks. Modern systems should use stronger hash functions like SHA-2 or SHA-3. However, SHA-1 remains acceptable for non-critical integrity checks or compatibility with legacy systems.
Conclusion
A SHA-1 generator provides a fast and straightforward way to compute 160-bit hashes for various applications, especially where legacy support is necessary. While its cryptographic security is outdated, its deterministic output and broad availability make it a useful tool for data verification and identification tasks in appropriate contexts. For enhanced security, transitioning to newer hash algorithms is strongly advised.